Introduction
Infrastructure as Code has transformed the way modern DevOps teams manage cloud environments. Among the most powerful features of Terraform is its module system. Terraform modules allow engineers to write reusable, maintainable, and production-ready infrastructure code. Instead of duplicating configuration across projects, you can create standardized building blocks that scale across environments.
If you are preparing for DevOps interviews or building real-world cloud projects, understanding Terraform modules is essential. In this guide, we will explore what modules are, how they are structured, the difference between root and child modules, best practices for reusable module design, how to pass variables into modules, and how to publish modules for team-wide usage.

What Are Terraform Modules?
A Terraform module is a container for multiple resources that are used together. Every Terraform configuration is technically a module. The configuration files in your working directory automatically form the root module.
Modules help you organize infrastructure into logical components. For example, instead of writing EC2 instances, security groups, and IAM roles in one large file, you can create a module specifically for a web server, another for a database layer, and another for networking.
Terraform modules provide abstraction. They allow you to hide internal implementation details while exposing only necessary inputs and outputs. This makes infrastructure easier to manage, test, and scale across multiple environments such as development, staging, and production.
In large organizations, modules enforce standardization. Teams can reuse approved infrastructure patterns instead of reinventing configurations every time.
Terraform Module Structure
A well-structured Terraform module follows a predictable layout. Although Terraform does not enforce a strict structure, industry best practices recommend separating configuration logically.
A typical module contains:
- main.tf – Defines the core resources.
- variables.tf – Declares input variables.
- outputs.tf – Exposes values for other modules.
- providers.tf – Configures required providers (optional in child modules).
- README.md – Documents usage and examples.
Keeping the structure clean improves readability and maintainability. It also helps new team members understand how the infrastructure is organized.
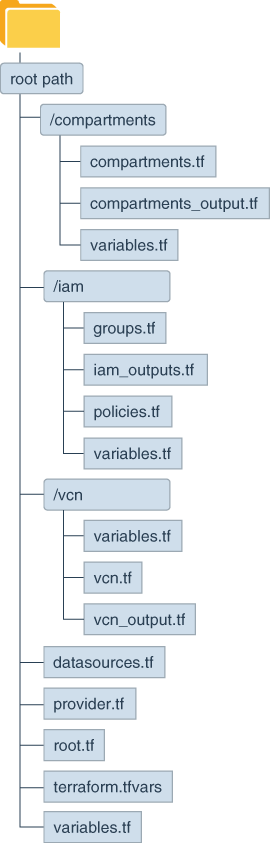
For enterprise-level projects, modules are often grouped inside a modules/ directory. Each module has its own subfolder. This makes version control and reuse straightforward.
Root Module vs Child Module
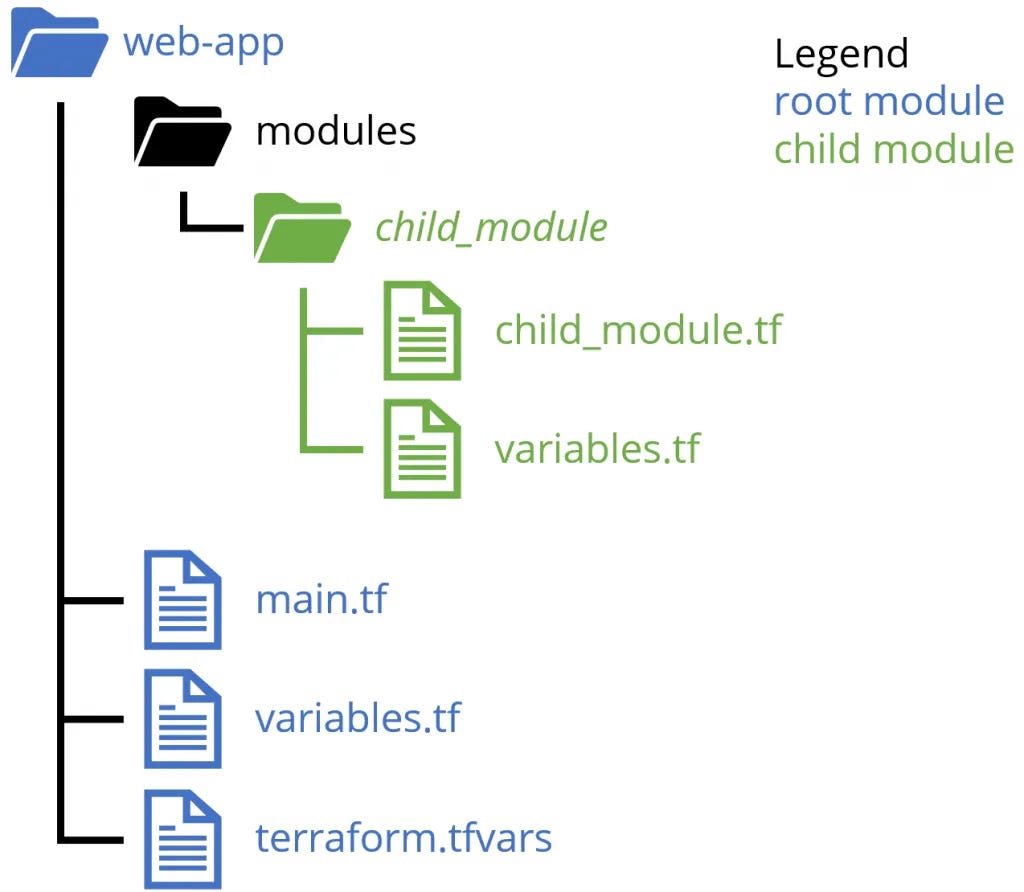
Understanding the difference between root and child modules is crucial for writing scalable Terraform code.
The root module is the working directory where you run Terraform commands such as terraform init, terraform plan, and terraform apply. It acts as the entry point of your infrastructure configuration.
A child module is any module that is called by another module. Child modules are referenced using the module block. They are designed to be reusable components.
The root module orchestrates the infrastructure by calling multiple child modules. For example, a root module might call:
- A VPC module
- A compute module
- A database module
This separation improves modularity. The root module focuses on composition, while child modules focus on implementation.
In production-grade infrastructure, this pattern keeps environments consistent while allowing flexible configuration through variable inputs.
Designing Reusable Terraform Modules
Reusable module design is the foundation of scalable Infrastructure as Code. A good module should be flexible, configurable, and environment-independent.
Avoid hardcoding values such as region names, instance types, or CIDR blocks. Instead, expose them as input variables. This ensures the module can be reused across multiple projects.
Keep modules focused on a single responsibility. A networking module should not create compute instances. A database module should not manage IAM policies unrelated to the database.
Documentation is equally important. Each module should clearly describe required variables, optional variables, outputs, and example usage. This improves adoption within teams.
Another best practice is versioning. When modules are versioned properly, teams can upgrade safely without breaking existing infrastructure.
Reusable design reduces duplication, lowers maintenance effort, and increases deployment reliability.
Passing Variables to Modules
Variables allow modules to remain dynamic and environment-aware. When you call a module, you pass arguments using the module block.
Inside the child module, variables are declared in variables.tf. In the root module, values are assigned when calling the module.
For example, instead of hardcoding an instance type inside the module, you declare a variable called instance_type. When calling the module from the root configuration, you pass the desired value.
This separation ensures that the same module can create small instances in development and larger instances in production without modifying internal code.
Outputs work similarly. A child module can expose values such as instance IDs or VPC IDs, which the root module or other modules can consume.
Passing variables and using outputs effectively enables loosely coupled infrastructure components.
Publishing Terraform Modules
Once your module is stable and reusable, you can publish it for wider usage.
Terraform modules can be:
- Stored locally inside a project repository
- Hosted in a private Git repository
- Published to the Terraform Registry
- Shared via version-controlled module repositories
The official HashiCorp Terraform Registry allows you to publish modules publicly so other developers can use them. When publishing, ensure that:
The module is well-documented.
Version tags follow semantic versioning.
Examples are included for clarity.
Variables and outputs are clearly defined.
For enterprise environments, private module registries are common. This ensures internal compliance, security, and standardization.
Publishing modules promotes collaboration and reduces repetitive infrastructure development across teams.
Why Terraform Modules Matter in Real-World DevOps
Terraform modules move infrastructure management from ad-hoc scripting to structured engineering. They encourage abstraction, consistency, and automation.
In cloud environments such as AWS, Azure, and Google Cloud, infrastructure often becomes complex. Modules help break that complexity into manageable components.
From a DevOps interview perspective, Terraform modules are frequently discussed. Interviewers expect candidates to understand root modules, child modules, variable passing, outputs, reusable design, and module versioning.
In real-world production environments, teams rely heavily on modular architecture to manage hundreds or thousands of resources safely.
Conclusion
Terraform modules are the backbone of scalable Infrastructure as Code. They allow you to write reusable, maintainable, and standardized infrastructure configurations. By mastering module structure, understanding root versus child modules, designing reusable components, passing variables effectively, and publishing modules responsibly, you transition from beginner-level Terraform usage to production-grade infrastructure engineering.
Organizations that adopt modular Terraform design achieve better maintainability, improved collaboration, and safer deployments. Whether you are building personal DevOps projects or managing enterprise cloud infrastructure, Terraform modules are an essential skill for long-term success.


